Build Tamper-Evident Verifiable Credentials to Combat Data Fraud
Verifiable Credentials offer a decentralised, tamper-evident framework that binds credentials to an individual's identity. This implementation guide covers the architecture, standards, and tools to get started.

Every developer has witnessed the same cycle. Organisations build systems to manage information, only to have them become targets for cyber-attacks. Concert tickets get counterfeited. Professional and academic certificates get forged. The harder organisations try to secure centralised systems, the more attractive they become to criminals.
This pattern repeats because the fundamental approach is flawed. Current centralised platforms collect excessive data stored in databases that become honey pots for cybercriminals. Meanwhile, individuals surrender control of their own credentials to platforms they must trust to protect their information.
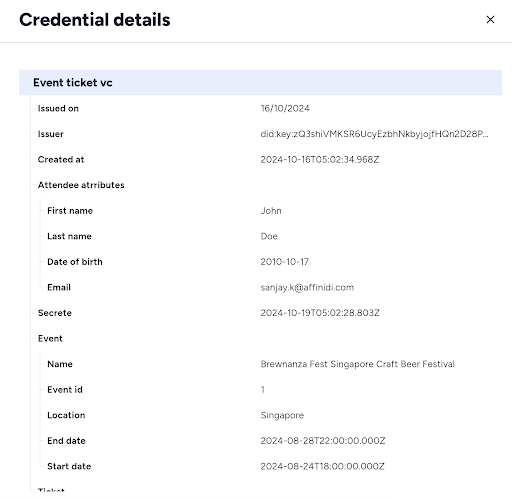
What if the entire model could be inverted? Verifiable Credentials (VCs) answer this challenge by offering a decentralised, tamper-evident framework that binds credentials to an individual’s identity securely and privately. Built on W3C standards, VCs are digital representations of claims like certificates, tickets, or identity details.
Why Current Systems Create Vulnerability
Traditional credential systems face persistent issues that VCs solve:
- Fraud and Counterfeiting: VCs offer tamper-evident, identity-bound credentials that are cryptographically signed and verifiable.

- Fragmented Experiences: VC-based systems provide a unified, cross-platform solution.
- Privacy Vulnerabilities: VCs allow individuals to share only essential information without revealing sensitive personal data unnecessarily.
The Architecture That Changes Everything
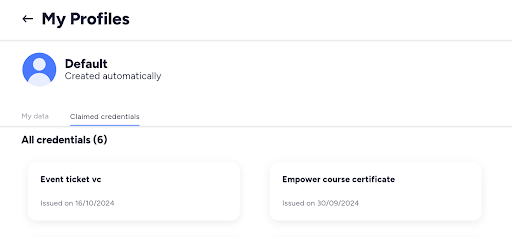
VCs enable individuals to manage their data with complete autonomy through selective disclosure. Credentials can be stored in personal data vaults such as the Affinidi Vault, giving individuals full control.
VC-based credential systems streamline the entire process:
- Unified Credential Management: Store all credentials in a single digital wallet.
- Cross-Platform Access: VCs work across devices and platforms.
- Offline Verification: Credentials can be verified without internet connection.
Understanding the Foundation
The VC ecosystem consists of three core entities:
- Issuer: The authority creating and issuing the credential.
- Holder: The individual controlling its use and determining how to share it.
- Verifier: The party that requests and validates the credential independently.
Implementing with OID4VCI
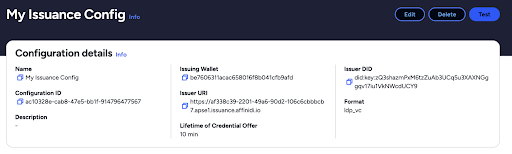
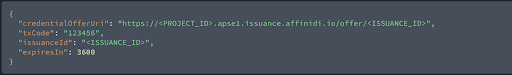
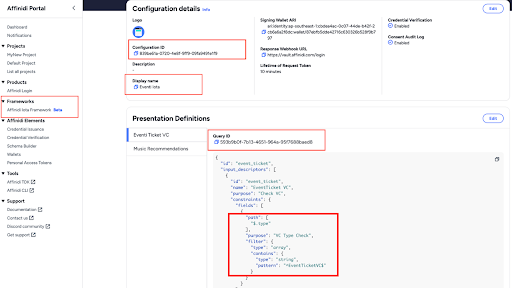
Open standards such as OpenID Connect for Verifiable Credential Issuance (OID4VCI) make secure issuance possible. Affinidi’s suite of solutions supports developers in implementing these open standards.
Key Components
Affinidi Elements provides:
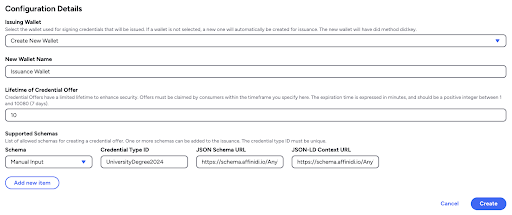
- Credential Issuance Service: Enables applications to issue credentials to users’ Affinidi Vault.
- Credential Verification Service: Verifies VCs and Verifiable Presentations for authenticity.
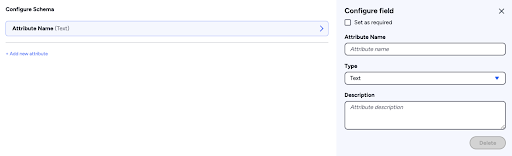
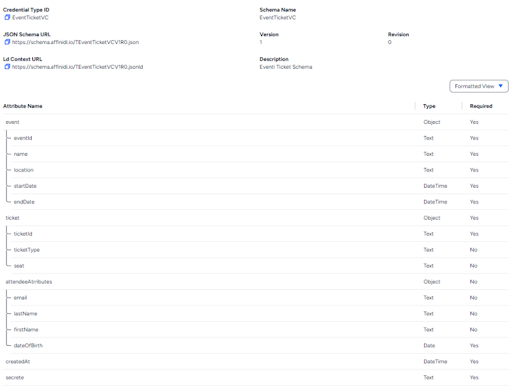
- Schema Builder: Creates schemas based on the W3C model.
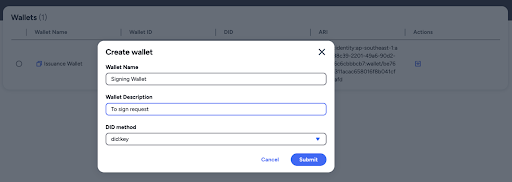
- Wallets: Sign and issue Verifiable Credentials.
The Complete Transformation
This implementation creates a system where security, privacy, and usability improve simultaneously. Individual privacy increases because people control their own data. Organisational security improves because there are no central databases to breach. System usability enhances because verification happens instantly.
The technology and standards exist today. The implementation is straightforward. Developers ready to begin can access comprehensive guides through the Affinidi Documentation.
Build with Affinidi
Start building trust infrastructure with our open-source tools and developer-friendly APIs.