Escape Vendor Lock-In, and Build for the Long Run with Open Standards
Open standards aren't a philosophy, they're a strategy. Learn how DIDs, DIDComm, and open protocols give you freedom from vendor lock-in in the age of autonomous AI agents.

The path into any major tech ecosystem is paved with convenience. But that convenience comes at a cost: vendor lock-in. You get easy access with proprietary APIs and seamless data formats, but the moment you need to change direction or scale outside the walls, you’re trapped. A developer’s worst nightmare is realising their infrastructure and data are no longer their own. The stakes are higher than ever, especially as AI systems become central to our operations. If your agents are exclusively tied to one cloud identity or one closed system, you are essentially outsourcing your long-term roadmap.
Open standards change that. This blog aims to find out what open standards look like in the age of autonomous agents.
This isn’t about blockchain hype or cryptocurrency speculation. This is about fundamental protocols that are reshaping how applications communicate, authenticate, and maintain trust, especially as we enter the era of autonomous AI agents that need to interact securely across organisational boundaries without human intervention.
The Open Standard Advantage
Think of how the internet and web flourished: because of open protocols like TCP/IP and HTTP. Similarly, an open API or open data format means any developer can swap in a different backend or tool without rewriting everything. For example, the ONNX model format is an open standard for AI models: if you train a neural network in PyTorch, you can export it to ONNX and deploy it in a totally different runtime or hardware environment.
Likewise, using open-source databases (PostgreSQL instead of a cloud-only datastore) or container orchestrators (Kubernetes) means your code isn’t chained to one vendor.
In short, open standards foster innovation and competition. They provide freedom of choice and longevity rather than short-term convenience.
Standards create freedom. They let you build without asking permission, and replace components without rewriting everything. Now the same shift is happening in AI.
Building Trustworthy AI Systems with Open Standards
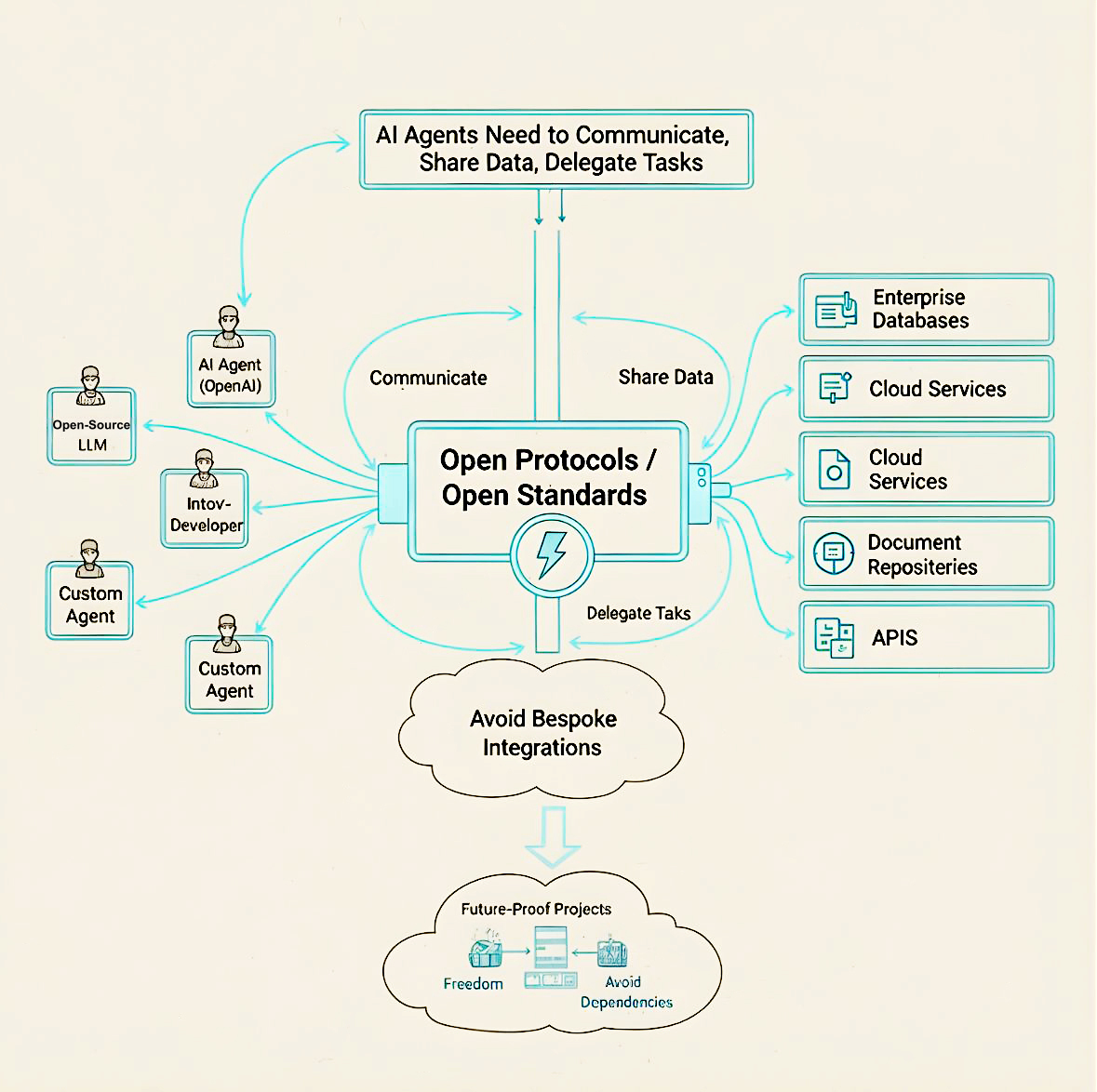
In agentic AI, open standards are a real advantage. Autonomous agents need to communicate, share data, and call services across platforms, and that only works with open protocols.
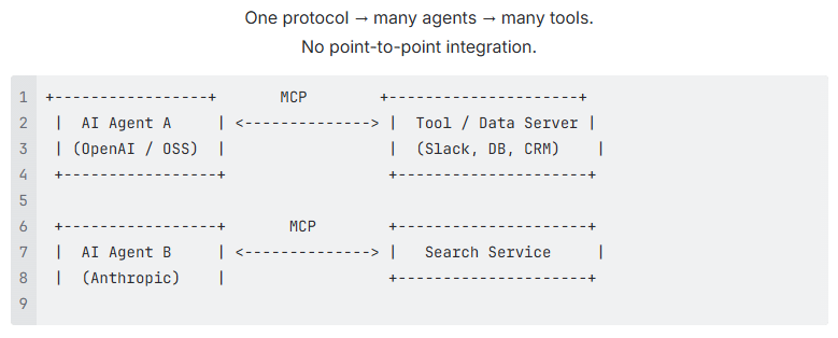
The Model Context Protocol (MCP) is a recent example: a JSON-RPC-style protocol that lets any agent fetch context or call tools from any service. It’s often described as a “USB-C for AI”.
One MCP server can be used by many AI agents.
- No custom integrations.
- No proprietary bridges.
- No vendor choke points.
Other emerging efforts, like Agent2Agent show the same trend: defining shared rules for how agents coordinate, delegate tasks, authenticate, and hand off work.
- When standards exist, ecosystems grow.
- When ecosystems grow, innovation accelerates.
- When innovation accelerates, everyone wins, not just the biggest cloud provider.
Agentic AI Needs More Than Intelligence. It Needs Trust.
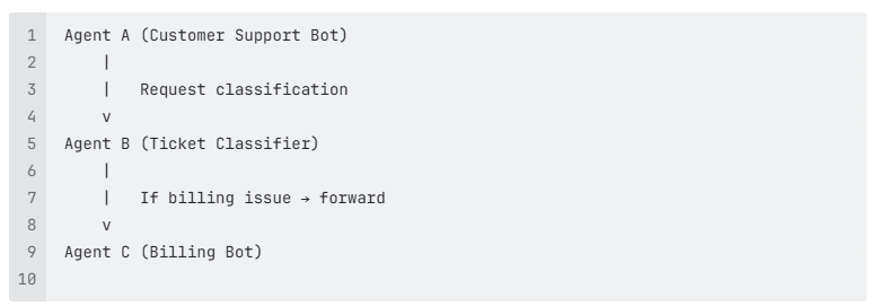
Autonomous AI agents don’t just generate text, they act.
- Fetch data
- Execute workflows
- Talk to other agents
- Make API calls
- Access enterprise systems
For this to work safely:
- Agents must prove who they are
- They must communicate securely
- They must share data without exposing raw personal information
- They must interoperate across vendors, clouds, and organisations
This is where open identity and messaging standards come in.
Digital Passports for Autonomous Systems
In a world run by autonomous agents, identity is paramount. Agents must prove who they are, communicate securely, and share data without exposing private information. This is where decentralised identity standards come in.
A Decentralised Identifier (DID) is a standard way to represent any entity’s identity on the Web without a central authority. Standards like W3C’s DIDs and the DIDComm protocol give AI agents and devices a way to prove who they are and talk securely.
In a DID-based system, each agent has a public DID and a corresponding private key. The DID Document lists things like public keys and service endpoints — the minimal data needed for others to communicate with that agent.
With DIDs:
- An AI agent can have its own identity, independent of a vendor.
- Its public keys are published in a DID Document.
- Anyone can verify its authenticity cryptographically.
Securing Agent Communication with DIDComm
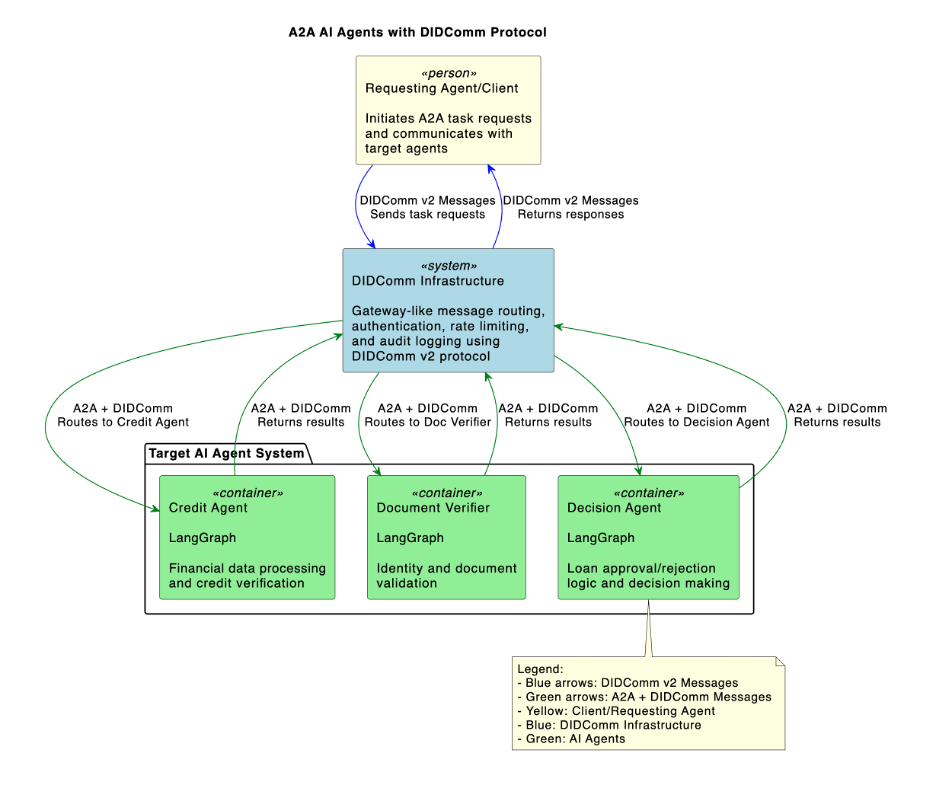
DIDComm takes this identity further: it’s an encrypted, peer-to-peer messaging protocol built on DIDs. Using DIDComm, one agent can send another an encrypted JSON message directly, peer-to-peer, without needing a siloed vendor API.
Because DIDComm is built atop DIDs and is transport-agnostic, it provides end-to-end encrypted, authenticated communication across virtually any medium. It abstracts the security and routing logic from the network infrastructure:
- Application Layer: Contains the agent logic and task execution (the message content).
- DIDComm Layer: Handles message encryption, cryptographic signing, and secure routing.
- Transport Layer: Facilitates the message exchange (e.g., Google A2A, IBM ACP, or a proprietary message broker).
- Network Layer: The underlying protocols used to move data (HTTP, gRPC, WebSockets, ZeroMQ, etc.).
This layering means:
- Agents authenticate each other cryptographically.
- All communication is end-to-end encrypted.
- Messages work over any common transport (HTTP, email, MQTT) without dependency on a proprietary cloud service.
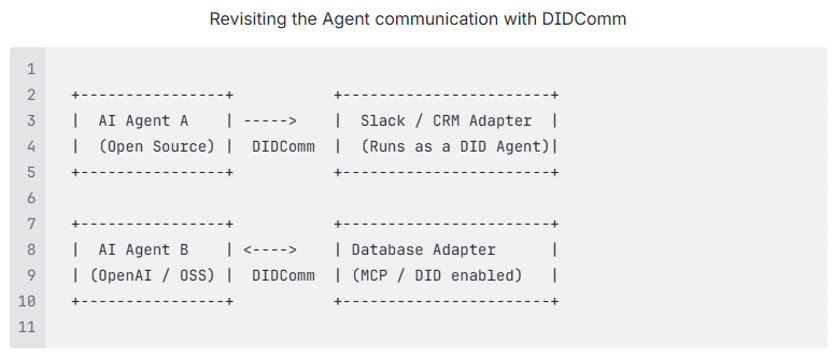
If you want agents to cooperate across companies and platforms, DIDComm gives you a secure common language.
Building for Forever
Open standards aren’t a philosophy, they’re a strategy.
- DIDs give agents portable, verifiable identity
- Verifiable Credentials enable selective, privacy-preserving trust
- DIDComm provides universal, encrypted messaging
- MCP standardises tool access and context
- Open-source implementations (like DIDComm Rust) prove it works today
If you want AI that is secure, interoperable, privacy-preserving, and not owned by a vendor, you build on open standards. Because the future isn’t just about intelligent systems, it’s about trustworthy ones. And trust only scales when no single company controls it.
Build with Affinidi
Start building trust infrastructure with our open-source tools and developer-friendly APIs.